Elevation rules
Elevation rules define what privileged actions are allowed or denied on endpoints. You can create file rules, publisher rules, or certificate rules.
Overview
File rule
- Rule that identifies a specific executable using
file hash,file name, and / orfile path. - Use this rule when you need to allow / deny a certain application.
- For example, using SHA256 file hash you can allow execution of a certain version of Google Chrome.
Publisher rule
- Rule that identifies a specific publisher by certificate thumbprint.
- Use this rule when you need to allow / deny anything signed by a certain publisher certificate.
- For example, you have a set of applications that your internal team develops and signs with a publisher certificate. When you create a rule using the certificate thumbprint, you can allow all applications signed by the certificate of you developer team.
Certificate rule
- Rule that identifies a verified publisher by certificate attributes.
- Use this rule when you want to allow / deny any application signed by any verified publisher certificate of a certain company.
- For example, Oracle uses various certificates to sign its binaries. You can create a rule to match
Oracle.*as an organization name in the verified publisher certificate. This way you can allow all Oracle executables, even if they are signed by different publisher certificates.
How to manage rules
Web portal
Today you can create rules from generated elevation events.
- Access your customer admin dashboard
- Navigate to
Elevation→Events - Click on
...and chooseCreate rule - The rule dialog will open with all details pre-populated

- To create a
file ruleselect any file attributes that you need. - To create a
publisher rule, you can check the certificate thumbprint area. For your context, we show you the publisher name and status (verified or not). - To create a
certificate rule, select any certificate attributes that you want to match.
💡
You can use regular expressions to match certain certificate attributes. For example, if you want to match all verified Microsoft certificates you can use Microsoft.* in the CN section.
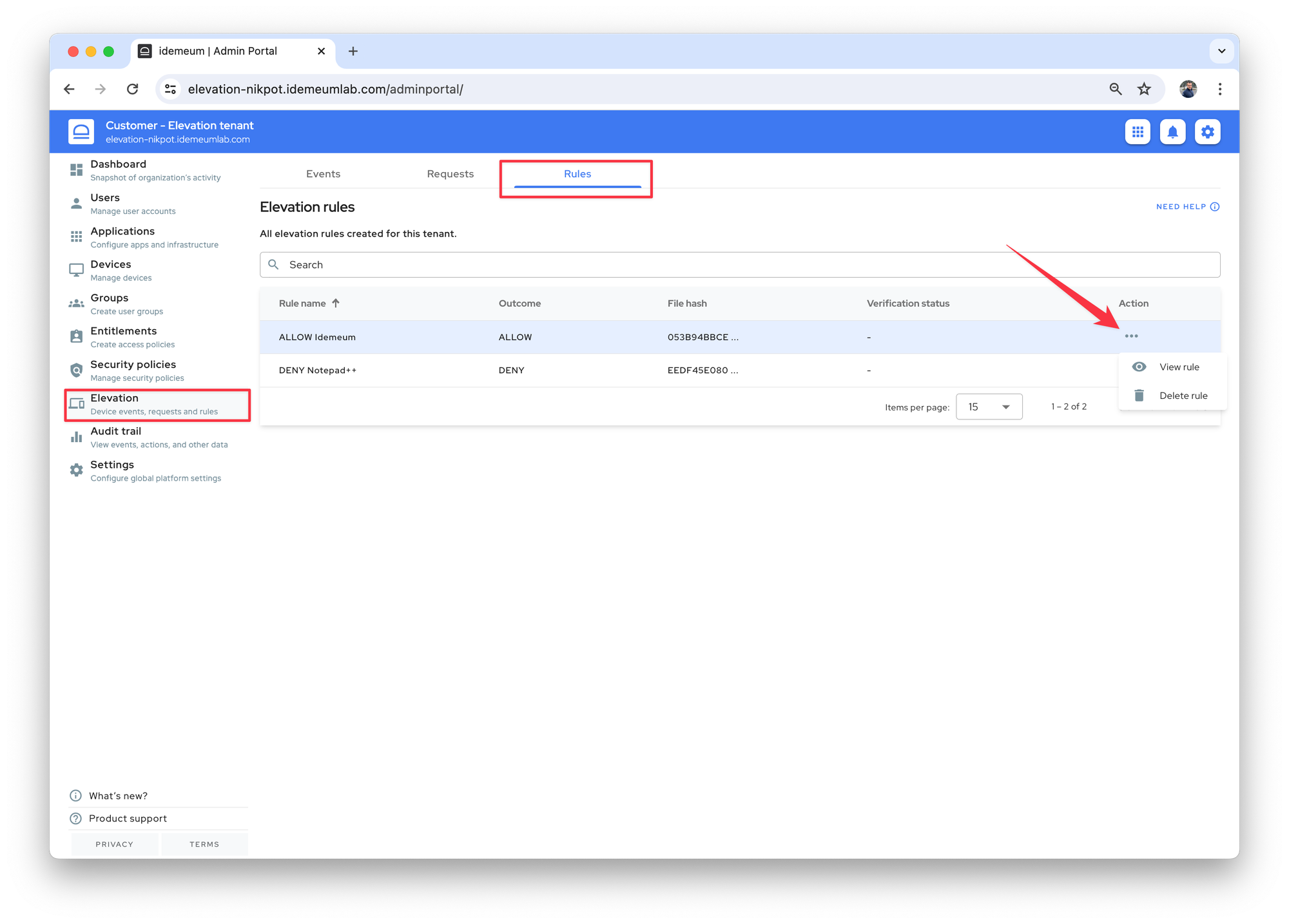
- To view or delete the rules, navigate to
Elevation→Rules - Click on
...and you canVieworDeletethe rule
Mobile application
- When approving or denying user requests with idemeum application you can automatically create rules.
- Choose
Approve for tenantwhen you want to create a rule. - Idemeum will automatically create
file ruleusing the executable SHA256 hash value. In the UI you will see the rule with the nameALLOW <app_name>, for exampleALLOW Google Chrome.